What if malware didn’t require an operating system to function? How would anyone possibly notice, let alone disable it?
The original article found on darkreading Read More
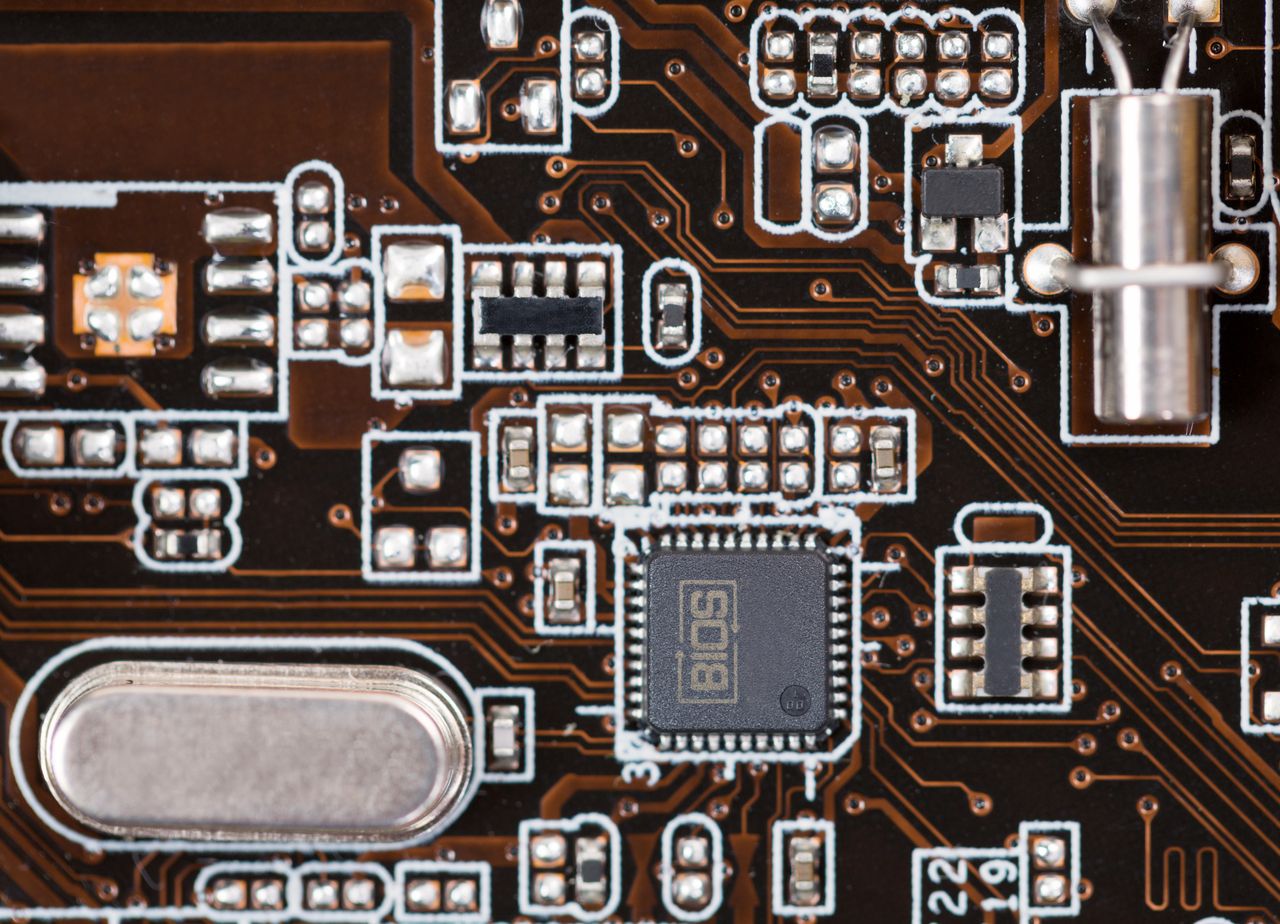
What if malware didn’t require an operating system to function? How would anyone possibly notice, let alone disable it?
The original article found on darkreading Read More