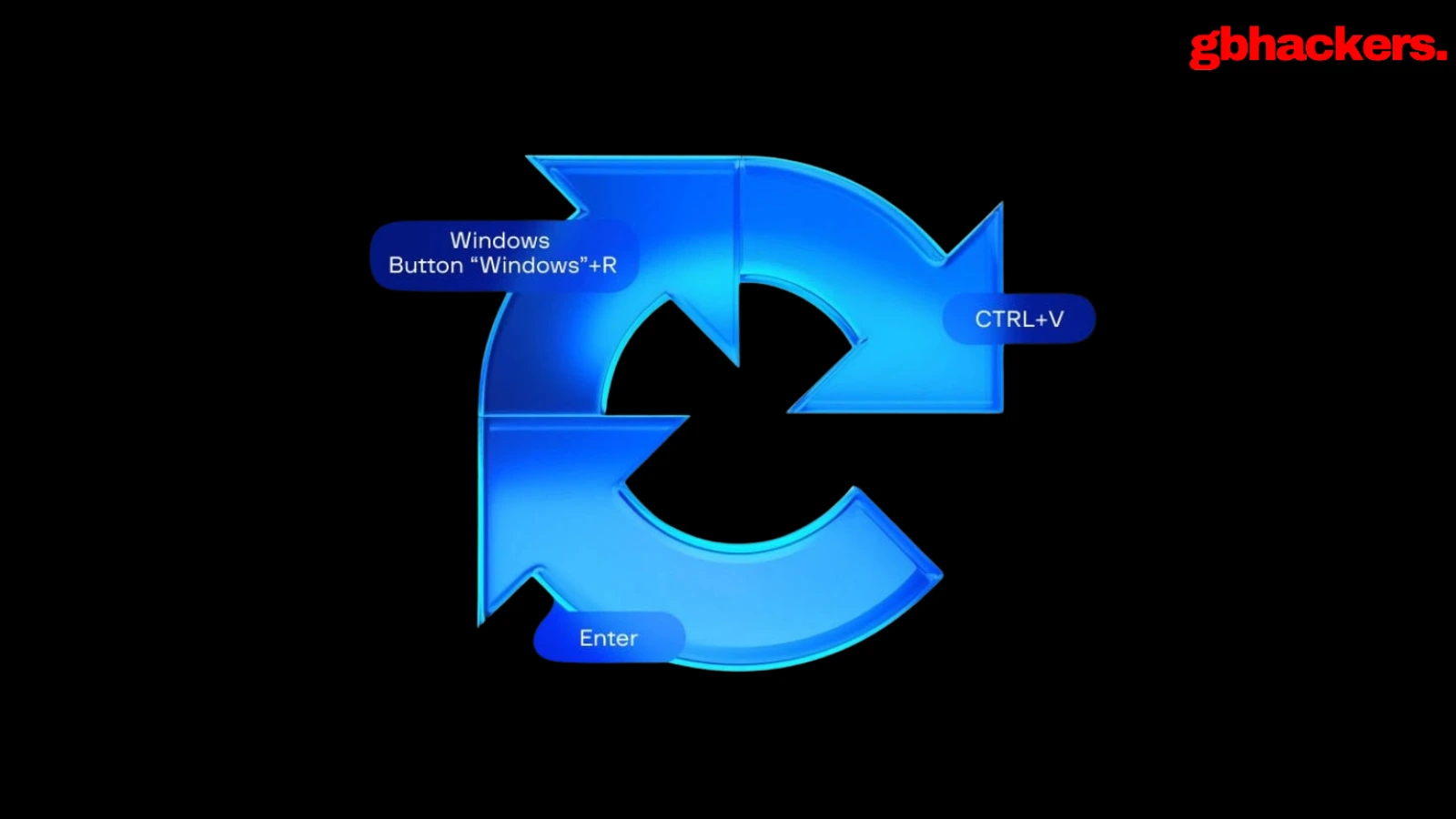
A refreshed ClickFix campaign that swaps macOS Terminal for Script Editor to deliver an Atomic Stealer payload to unsuspecting Mac users quietly. By abusing the applescript:// URL scheme, attackers sidestep Apple’s new paste-protection in Terminal on macOS Tahoe 26.4 while preserving the same underlying “click-to-fix” social engineering pattern. Traditional ClickFix chains rely on fake support or “system cleanup” pages […]
The post ClickFix Campaign Abuses macOS Script Editor to Deploy Atomic Stealer appeared first on GBHackers Security | #1 Globally Trusted Cyber Security News Platform.
The original article found on GBHackers Security | #1 Globally Trusted Cyber Security News Platform Read More