Aus Sicht von Forrester bleibt die Lage für IT-(Sicherheits-)Entscheider auch 2026 angespannt. Maya Lab /Shutterstock Keine Entwarnung für IT-(Sicherheits-)Entscheider: Die Analysten von Forrester gehen in […]
Author: cyberbytes
Google researchers detect first operational use of LLMs in active malware campaigns
Threat actors are now actively deploying AI-enabled malware in their operations. Google Threat Intelligence Group (GTIG) has identified cybercriminal use of “just-in-time” AI which employs […]
APT ‘Bronze Butler’ Exploits Zero-Day to Root Japan Orgs
A critical security issue in a popular endpoint manager (CVE-2025-61932) allowed Chinese state-sponsored attackers to backdoor Japanese businesses. The original article found on darkreading Read […]
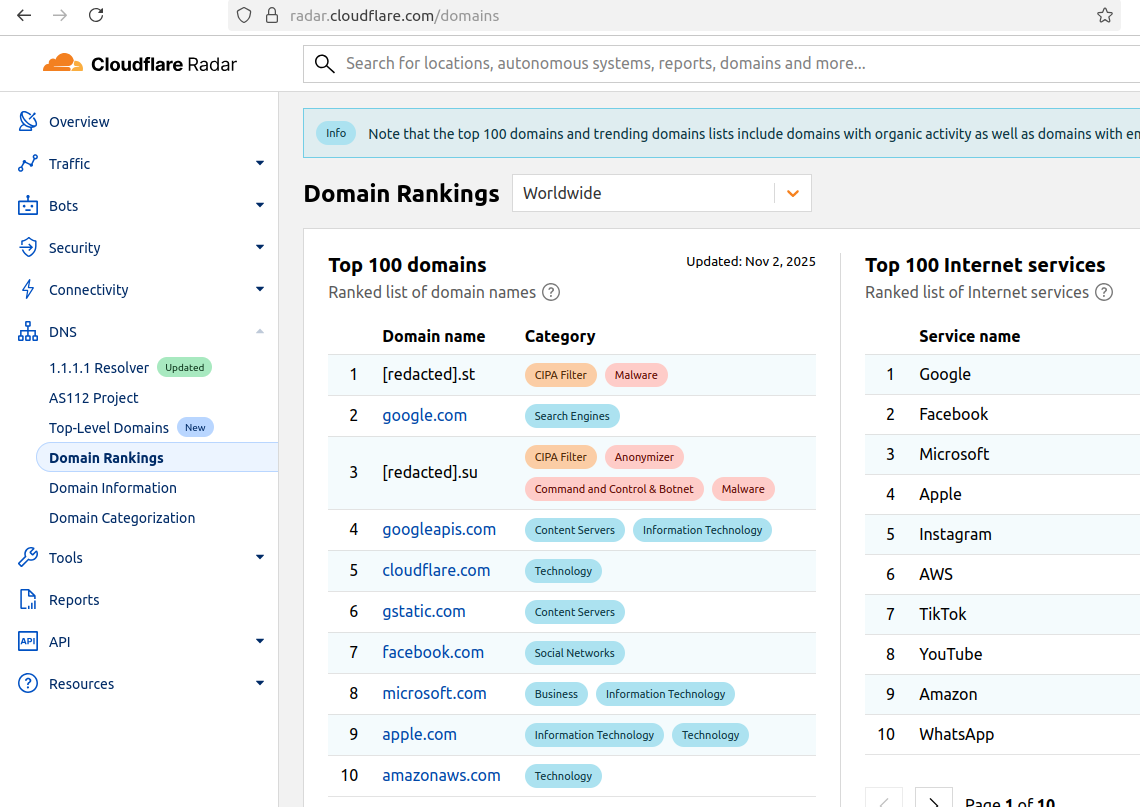
Cloudflare Scrubs Aisuru Botnet from Top Domains List
For the past week, domains associated with the massive Aisuru botnet have repeatedly usurped Amazon, Apple, Google and Microsoft in Cloudflare’s public ranking of the […]
Nikkei Suffers Breach Via Slack Compromise
The Japanese media giant said thousands of employee and business partners were impacted by an attack that compromised Slack account data and chat histories. The […]
Russian APT abuses Windows Hyper-V for persistence and malware execution
Cyberespionage groups are always looking for novel ways to establish covert and long-term persistent access to compromised systems. The latest example comes from a Russian […]
WordPress plugin hole enables account takeover
The disclosure of a major security hole within a popular WordPress email plugin is a reminder to CISOs about the risks posed by relatively unsupervised […]
Office sandbox file security to disappear from enterprise Windows by late 2027, Microsoft confirms
Windows enterprise administrators will have until December 2027 at the latest to put in place alternatives to the security protection offered by Microsoft Defender Application […]
Google Uncovers PROMPTFLUX Malware That Uses Gemini AI to Rewrite Its Code Hourly
Google on Wednesday said it discovered an unknown threat actor using an experimental Visual Basic Script (VB Script) malware dubbed PROMPTFLUX that interacts with its […]
Closing the AI Execution Gap in Cybersecurity — A CISO Framework
CISOs must navigate five critical dimensions of AI in cybersecurity: augmenting security with AI, automating security with AI, protecting AI systems, defending against AI-powered threats, […]