The ransomware landscape underwent significant disruption, marked by the abrupt cessation of operations from several prominent Ransomware-as-a-Service (RaaS) groups, including RansomHub, Babuk-Bjorka, FunkSec, BianLian, 8Base, […]
Author: cyberbytes
Storm-2603 Deploys Custom Malware Using BYOVD to Bypass Endpoint Protections
Check Point Research (CPR) has delved into the operations of Storm-2603, a recently identified threat actor linked to Chinese advanced persistent threat (APT) groups, amid […]
Lazarus Hackers Weaponize 234 npm and PyPI Packages to Infect Developers
Sonatype’s automated detection systems have uncovered an expansive and ongoing infiltration of the global open-source ecosystem by the notorious Lazarus Group, a threat actor believed […]
Attackers Use Fake OAuth Apps with Tycoon Kit to Breach Microsoft 365 Accounts
Cybersecurity researchers have detailed a new cluster of activity where threat actors are impersonating enterprises with fake Microsoft OAuth applications to facilitate credential harvesting as […]
Building the Perfect Post-Security Incident Review Playbook
By creating a safe environment for open discussion, prioritizing human context alongside technical data, and involving diverse stakeholders, organizations can turn security incidents into accelerators […]
Male-Dominated Cyber Industry Still Holds Space for Women With Resilience
When trying to crack your way into a cyber career, true passion and a bold love of the industry is a must, if you want […]
Hackers Exploit Microsoft 365’s Direct Send Feature for Internal Phishing Attacks
Threat actors are leveraging Microsoft 365’s Direct Send feature to launch sophisticated phishing campaigns that mimic internal organizational emails, eroding trust and heightening the success […]
Chinese Threat Actors Hack 11,000 Android Devices to Deploy PlayPraetor Malware
Chinese-speaking threat actors have used the PlayPraetor Remote Access Trojan (RAT) to infiltrate more than 11,000 Android devices globally in a sophisticated Malware-as-a-Service (MaaS) operation. […]
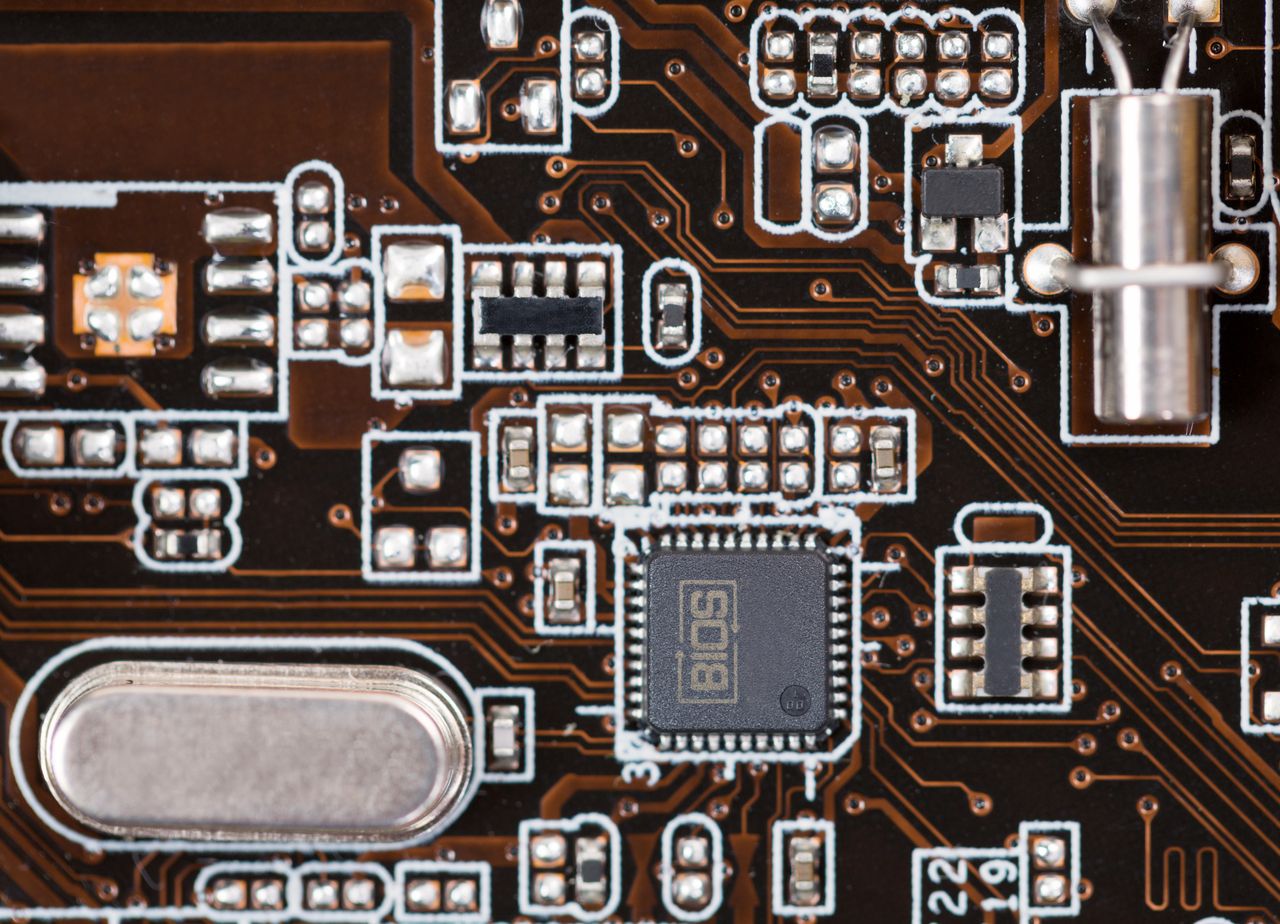
New ‘Shade BIOS’ Technique Beats Every Kind of Security
What if malware didn’t require an operating system to function? How would anyone possibly notice, let alone disable it? The original article found on darkreading […]
Blizzard Group’s ApolloShadow Malware Installs Root Certificates to Trust Malicious Sites
Microsoft Threat Intelligence has exposed a sophisticated cyberespionage operation orchestrated by the Russian state-sponsored actor tracked as Secret Blizzard, which has been actively compromising foreign […]




_Yee_Xin_Tan_Alamy.jpg?width=1280&auto=webp&quality=80&disable=upscale)