Security researchers have confirmed active exploitation attempts targeting the critical authentication bypass vulnerability in CrushFTP (CVE-2025-2825) following the public release of proof-of-concept exploit code. Based […]
Author: cyberbytes
Apple Warns of Three 0-Day Vulnerabilities Actively Exploited in Attacks
Apple has issued an urgent security advisory concerning three critical zero-day vulnerabilities CVE-2025-24200, CVE-2025-24201, and CVE-2025-24085 that have been actively exploited in sophisticated attacks. These […]
Microsoft Uncovers Several Vulnerabilities in GRUB2, U-Boot, Barebox Bootloaders Using Copilot
Microsoft has discovered multiple critical vulnerabilities affecting widely used bootloaders including GRUB2, U-Boot, and Barebox. These security flaws potentially expose systems to sophisticated boot-level attacks […]
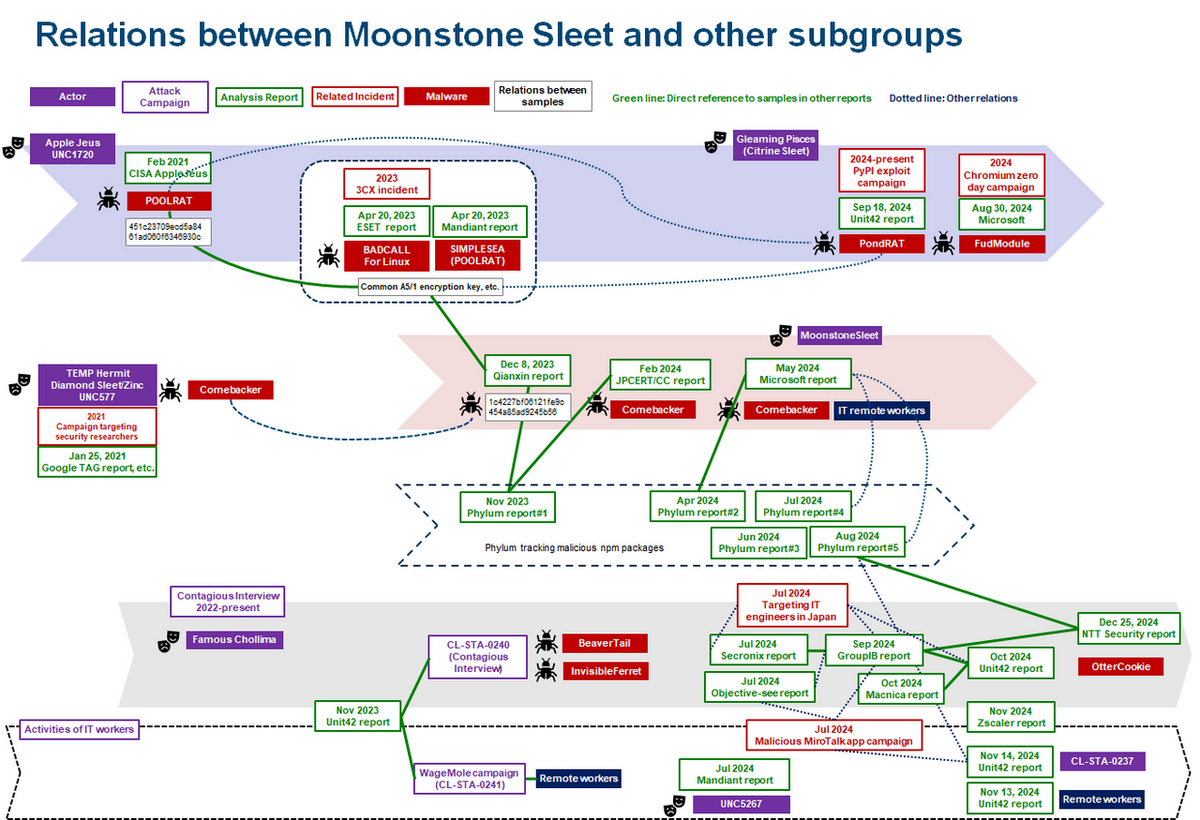
Lazarus Group is No Longer Consider a Single APT Group, But Collection of Many Sub Groups
The cybersecurity landscape is witnessing a growing complexity in the attribution of Advanced Persistent Threat (APT) actors, particularly the North Korean-linked Lazarus group. Once considered […]
Hackers Scanning From 24,000 IPs to Gain Access to Palo Alto Networks GlobalProtect Portals
Researchers have detected an alarming surge in malicious scanning activity targeting Palo Alto Networks’ GlobalProtect VPN portals. Over a 30-day period, nearly 24,000 unique IP […]
Apple Fined €150 Million by French Regulator Over Discriminatory ATT Consent Practices
Apple has been hit with a fine of €150 million ($162 million) by France’s competition watchdog over the implementation of its App Tracking Transparency (ATT) […]
CoffeeLoader Malware Is Stacked With Vicious Evasion Tricks
Next-level malware represents a new era of malicious code developed specifically to get around modern security software like digital forensics tools and EDR, new research […]
Oracle Cloud Users Urged to Take Action
Although Oracle has denied its cloud infrastructure services were breached, security experts recommend Oracle customers independently verify if they were affected and take measures to […]
DoJ Seizes Over $8M from Sprawling Pig Butchering Scheme
The department was able to trace the stolen funds to three main cryptocurrency accounts after being routed through a series of other platforms. The original […]
Russian Hackers Exploit CVE-2025-26633 via MSC EvilTwin to Deploy SilentPrism and DarkWisp
The threat actors behind the zero-day exploitation of a recently-patched security vulnerability in Microsoft Windows have been found to deliver two new backdoors called SilentPrism […]
.webp)