The botnet malware known as RondoDox has been observed targeting unpatched XWiki instances against a critical security flaw that could allow attackers to achieve arbitrary […]
Author: cyberbytes
Five U.S. Citizens Plead Guilty to Helping North Korean IT Workers Infiltrate 136 Companies
The U.S. Department of Justice (DoJ) on Friday announced that five individuals have pleaded guilty to assisting North Korea’s illicit revenue generation schemes by enabling […]
Was ist Social Engineering?
Mit Social-Engineering-Techniken manipulieren Cyberkriminelle die menschliche Psyche. Lesen Sie, wie das funktioniert und wie Sie sich schützen können. sp3n | shutterstock.com Selbst wenn Sie bei […]
From detection to response: Why confidence is the real game changer
Cybersecurity often feels like a race where you don’t know when the starting gun will fire. The moment a threat slips past the perimeter, the […]
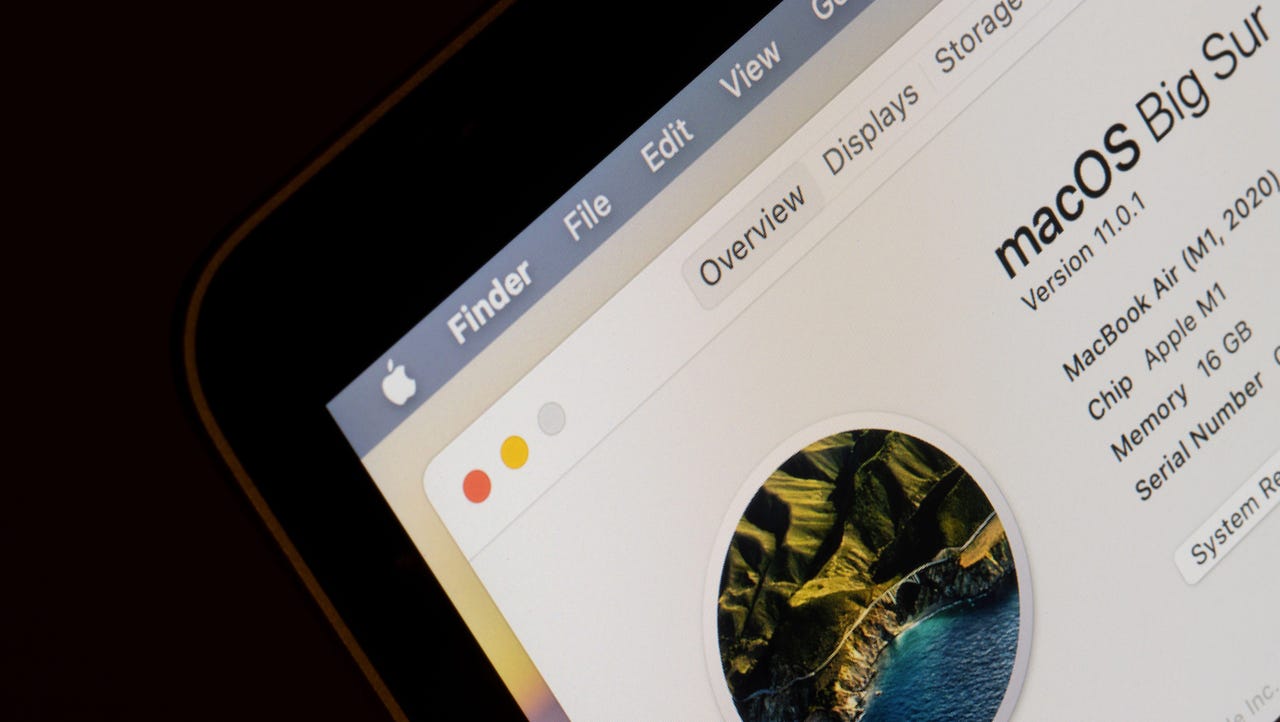
New Security Tools Target Growing macOS Threats
A public dataset and platform-agnostic analysis tool aim to help organizations in the fight against Apple-targeted malware, which researchers say has lacked proper attention. The […]
Akira RaaS Targets Nutanix VMs, Threatens Critical Orgs
The Akira ransomware group has been experimenting with new tools, bugs, and attack surfaces, with demonstrated success in significant sectors. The original article found on […]
150,000 Packages Flood NPM Registry in Token Farming Campaign
A self-replicating attack led to a tidal wave of malicious packages in the NPM registry, targeting tokens for the tea.xyz protocol. The original article found […]
Hardened Containers Look to Eliminate Common Source of Vulnerabilities
A kitchen-sink approach to building containers has loaded many with vulnerabilities. A handful of companies are trying to slim them down to address the issue. […]
Shadow Program Gives AWS Exec New Security Lens
Sara Duffer highlights the top lessons she brought back to her security role following three years in Amazon’s shadow program. The original article found on […]
North Korean Hackers Turn JSON Services into Covert Malware Delivery Channels
The North Korean threat actors behind the Contagious Interview campaign have once again tweaked their tactics by using JSON storage services to stage malicious payloads. […]