Microsoft has detailed how organizations can detect and mitigate a recent supply chain compromise involving malicious Axios npm releases and infrastructure attributed to the North […]
Category: Cyber Security News
Cybersecurity in the age of instant software
AI is rapidly changing how software is written, deployed, and used. Trends point to a future where AIs can write custom software quickly and easily: […]
FBI Warns Chinese Mobile Apps Could Expose User Data to Cyberattacks
The Federal Bureau of Investigation (FBI) has issued a public warning about potential data security risks associated with foreign-developed mobile applications, particularly those developed by […]
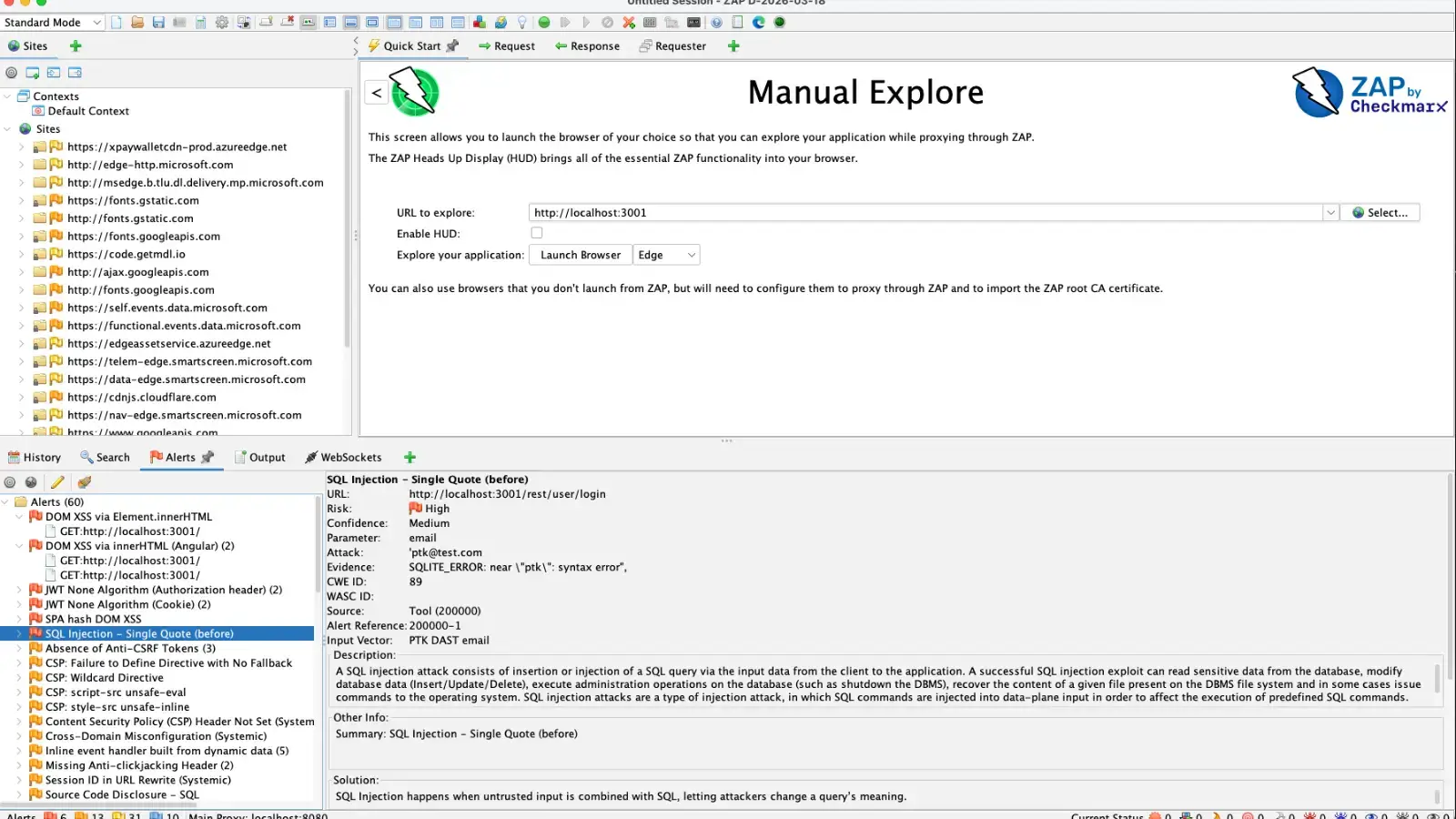
New ZAP PTK Add-On Converts Browser Security Findings Into Native ZAP Alerts
The OWASP Zed Attack Proxy (ZAP) just received a massive upgrade for testing modern web applications. The release of the ZAP PTK Add-on 0.3.0, working […]
Cisco Smart Software Manager Flaw Allowed Arbitrary Command Execution
Cisco has released a high-priority security advisory regarding a critical vulnerability in its Smart Software Manager On-Prem (SSM On-Prem) platform. The flaw, tracked as CVE-2026-20160, […]
Critical PX4 Autopilot Vulnerability Let Attackers Gain Control of Drones
The Cybersecurity and Infrastructure Security Agency (CISA) has issued a high-priority alert regarding a severe vulnerability in the PX4 Autopilot system. This critical flaw could […]
TA416 Broadens Europe Spy Campaign With Web Bugs and Malware
China-aligned threat actor TA416 has resumed large-scale espionage against European governments. It is now expanding to Middle Eastern diplomatic targets, combining web bug reconnaissance with […]
WhatsApp Attack Chain Delivers VBS, Cloud Payloads, MSI Backdoor
A new malware campaign that abuses WhatsApp messages to deliver malicious Visual Basic Script (VBS) files to Windows users, enabling persistent remote access through unsigned […]
Cisco Warns of Critical IMC Vulnerability Enabling Authentication Bypass
Cisco has published an urgent security advisory for CVE-2026-20093, a critical 9.8-severity authentication bypass vulnerability affecting its Integrated Management Controller (IMC) software. This high-risk flaw […]
Remcos RAT Attack Uses Obfuscated Scripts, Trusted Windows Tools
Remcos RAT operators are abusing obfuscated scripts and trusted Windows binaries to deliver a stealthy, largely fileless infection chain that runs almost entirely in memory […]