Thursday. Another week, another batch of things that probably should’ve been caught sooner but weren’t. This one’s got some range — old vulnerabilities getting new life, a […]
Category: Cyber Security News
Weak at the seams
Before I ever held a security title, I was a software engineer implementing vertically integrated automation systems for industrial manufacturing, warehouse-scale conveyor networks, robotic material […]
New Phishing Campaign Exploits Google Storage to Deliver Remcos RAT
A recently observed phishing campaign is abusing Google Cloud Storage to deliver the Remcos remote access trojan (RAT), relying on trusted Google infrastructure and a […]
New ClickFix variant bypasses Apple safeguards with one‑click script execution
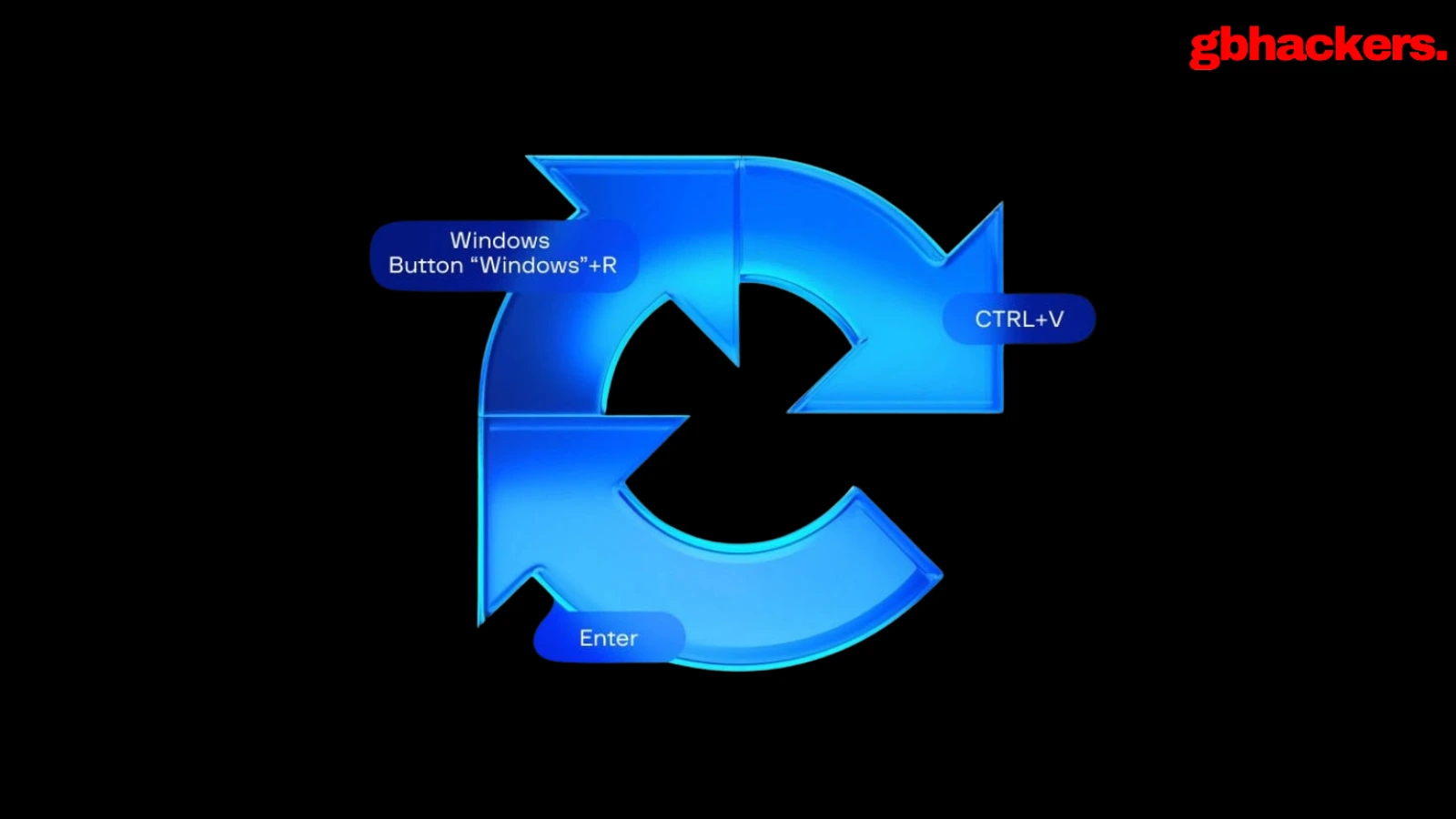
ClickFix malware campaigns are evolving again, with threat actors removing one of their most obvious and user‑dependent steps: convincing victims to paste malicious commands into […]
The Hidden Security Risks of Shadow AI in Enterprises
As AI tools become more accessible, employees are adopting them without formal approval from IT and security teams. While these tools may boost productivity, automate tasks, or […]
ClickFix Campaign Abuses macOS Script Editor to Deploy Atomic Stealer
A refreshed ClickFix campaign that swaps macOS Terminal for Script Editor to deliver an Atomic Stealer payload to unsuspecting Mac users quietly. By abusing the applescript:// URL scheme, attackers […]
ClickFix, Malicious DMGs Push notnullOSX to macOS Users
Hackers are abusing ClickFix commands and booby-trapping DMG installers to deliver a new macOS stealer called notnullOSX, built to loot high-value crypto wallets from Mac […]
Keeper Security Expands PAM Browser Isolation to Support Advanced Web Browsing Workflows
Keeper Security has announced the release of new Remote Browser Isolation (RBI) capabilities within KeeperPAM, delivering major adoption and usability improvements for modern web workflows […]
Patch windows collapse as time-to-exploit accelerates
The gap between vulnerability disclosure and exploitation is drastically decreasing, putting security teams’ patching practices on notice. According to Rapid7’s latest Cyber Threat Landscape Report, […]
Weak at the seams
Before I ever held a security title, I was a software engineer implementing vertically integrated automation systems for industrial manufacturing, warehouse-scale conveyor networks, robotic material […]