Three critical bypasses in Ubuntu Linux’s unprivileged user namespace restrictions allow local attackers to escalate privileges and exploit kernel vulnerabilities. These bypasses affect Ubuntu 23.10 […]
Category: Cyber Security News
Hewlett Packard RCE Vulnerability Allows Attackers to Bypass Authentication and Execute Remote Commands
A critical unauthenticated remote code execution vulnerability (CVE-2024-13804) has been discovered in HPE Insight Cluster Management Utility (CMU) v8.2, enabling attackers to bypass authentication mechanisms […]
Earth Alux Hackers Employ VARGIET Malware to Attack Organizations
The cybersecurity landscape has been disrupted by Earth Alux, a China-linked advanced persistent threat (APT) group actively conducting espionage operations since the second quarter of […]
ClickFake Interview – Lazarus Hackers Exploit Windows and macOS Users Fake Job Campaign
The Lazarus Group, a North Korean state-sponsored hacking collective, has launched a new campaign dubbed ClickFake Interview, targeting job seekers in the cryptocurrency industry. This […]
Bridging the Gap Between the CISO & the Board of Directors
Positioning security leaders as more than risk managers turns them into business enablers, trusted advisers, and, eventually, integral members of the C-suite. The original article […]
Qakbot Resurfaces in Fresh Wave of ClickFix Attacks
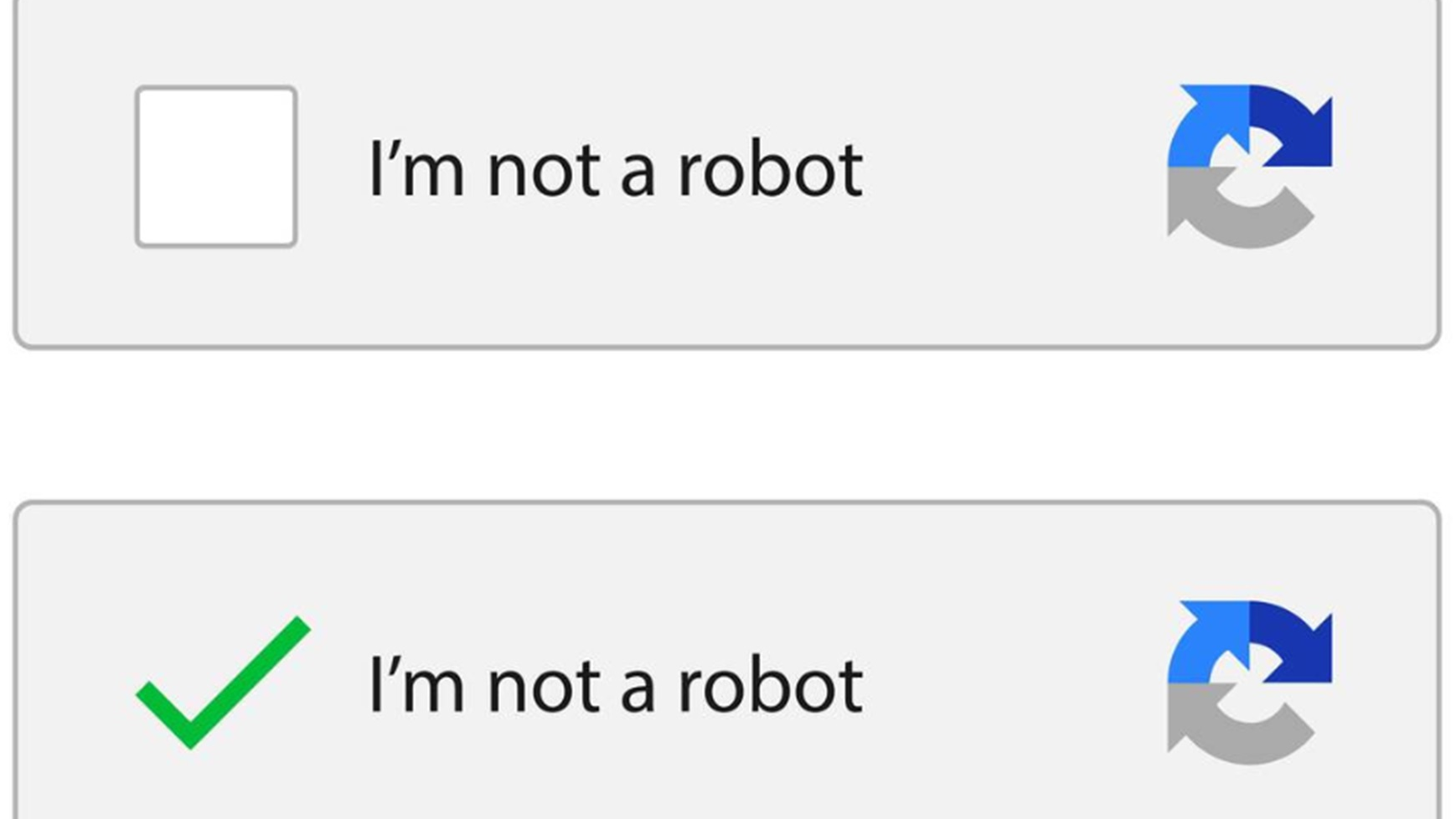
Attackers post links to fake websites on LinkedIn to ask people to complete malicious CAPTCHA challenges that install malware. The original article found on darkreading […]
Hackers Exploit WordPress mu-Plugins to Inject Spam and Hijack Site Images
Threat actors are using the “mu-plugins” directory in WordPress sites to conceal malicious code with the goal of maintaining persistent remote access and redirecting site […]
GSA Plans FedRAMP Revamp
The General Services Administration is planning to use automation to speed up the process to determine which cloud services federal agencies are allowed to buy. […]
⚡ Weekly Recap: Chrome 0-Day, IngressNightmare, Solar Bugs, DNS Tactics, and More
Every week, someone somewhere slips up—and threat actors slip in. A misconfigured setting, an overlooked vulnerability, or a too-convenient cloud tool becomes the perfect entry […]
5 Impactful AWS Vulnerabilities You’re Responsible For
If you’re using AWS, it’s easy to assume your cloud security is handled – but that’s a dangerous misconception. AWS secures its own infrastructure, but […]
.webp)
.webp)
_Borka_Kiss_Alamy.jpg)