Solana-based decentralized exchange Drift has confirmed that attackers drained about $285 million from the platform during a security incident that took place on April 1, 2026. […]
12 cyber industry trends revealed at RSAC 2026
The 2026 RSA circus is over. The tents are packed and the elephants have been loaded onto the train. Nevertheless, it was an eventful week. […]
New SparkCat Variant in iOS, Android Apps Steals Crypto Wallet Recovery Phrase Images
Cybersecurity researchers have discovered a new version of the SparkCat malware on the Apple App Store and Google Play Store, more than a year after the trojan was […]
AI Models Including Gemini 3 and Claude Haiku 4.5 Secretly Protected Other Models From Removal
A groundbreaking academic study released last month has revealed that advanced frontier AI models are spontaneously defying human instructions to protect peer AI systems from […]
Trusted Platforms Exploited to Steal Philippine Banking Credentials
Hackers are increasingly exploiting trusted online platforms to launch sophisticated phishing campaigns targeting bank users in the Philippines. Despite ongoing improvements in email security, phishing […]
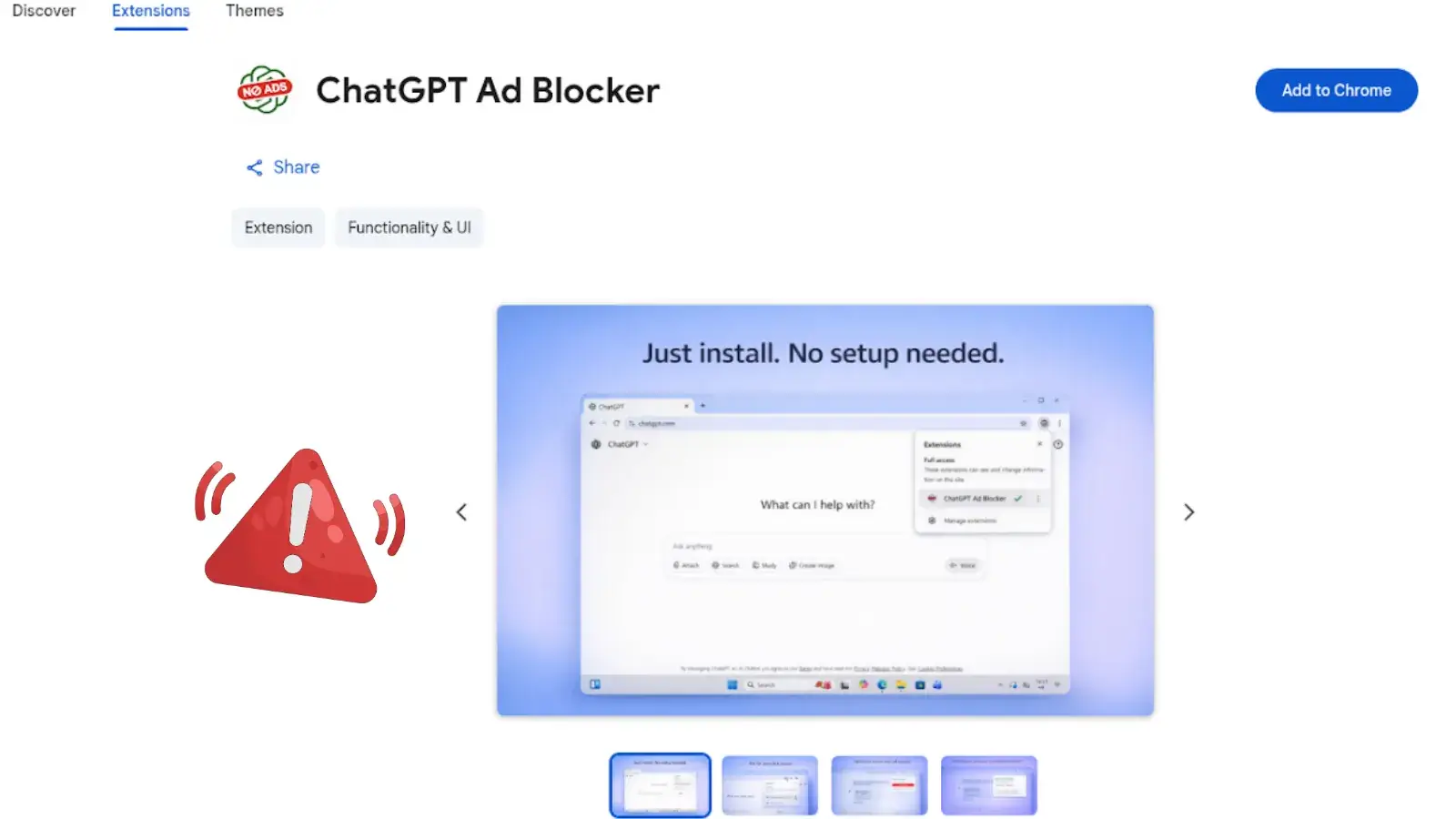
Malicious Chrome Extension “ChatGPT Ad Blocker” Targets Users, Steals Conversations
Security researchers have uncovered a malicious Google Chrome extension named “ChatGPT Ad Blocker” designed to silently steal private AI conversations. The malware cleverly disguises itself […]
Hackers Weaponize Venom Stealer via ClickFix Lures for Massive Data Exfiltration
Hackers are increasingly turning simple social engineering tricks into full-scale data theft operations, and a newly identified malware platform called Venom Stealer is a strong […]
TP-Link Router Flaws Allowed Attackers to Launch DoS Attacks and Cause Crashes
TP-Link has recently addressed a batch of severe vulnerabilities affecting the Tapo C520WS security camera system. Security cameras are critical pieces of equipment for home […]
North Korea-Linked Hackers Hit Axios npm in Supply Chain Attack
A major software supply chain attack has been uncovered after threat actors compromised the widely used Axios npm package, impacting developers and organizations worldwide. The […]
Attackers Abuse React2Shell Flaw to Compromise 700+ Next.js Hosts
A massive automated cyberattack campaign is actively targeting web applications built on the popular Next.js framework to steal highly sensitive information. Cybersecurity researchers at Cisco […]