The notorious Danabot banking malware has made a comeback with the release of version 669, marking a significant return after nearly six months of silence […]
CISA Issues Alert on Samsung 0-Day RCE Flaw Actively Exploited in Attacks
The Cybersecurity and Infrastructure Security Agency (CISA) has added a critical remote code execution vulnerability affecting Samsung mobile devices to its Known Exploited Vulnerabilities (KEV) […]
OWASP Top 10 2025 Released: Major Revisions and Two New Security Classes Added
The Open Web Application Security Project (OWASP) has officially unveiled the eighth edition of its influential Top 10 security risks list for 2025, introducing significant […]
Threat Report: xHunt Targets Microsoft Exchange and IIS with Custom Backdoors
The xHunt advanced persistent threat group continues to pose a significant cybersecurity risk through sophisticated attacks targeting Microsoft Exchange and IIS web servers with custom-built […]
Hackers Exploit Triofox 0-Day to Deploy Malicious Payloads Using Anti-Virus Feature
Cybersecurity researchers from Mandiant Threat Defense have uncovered a critical zero-day vulnerability in Gladinet’s Triofox file-sharing platform that allowed attackers to bypass authentication and execute […]
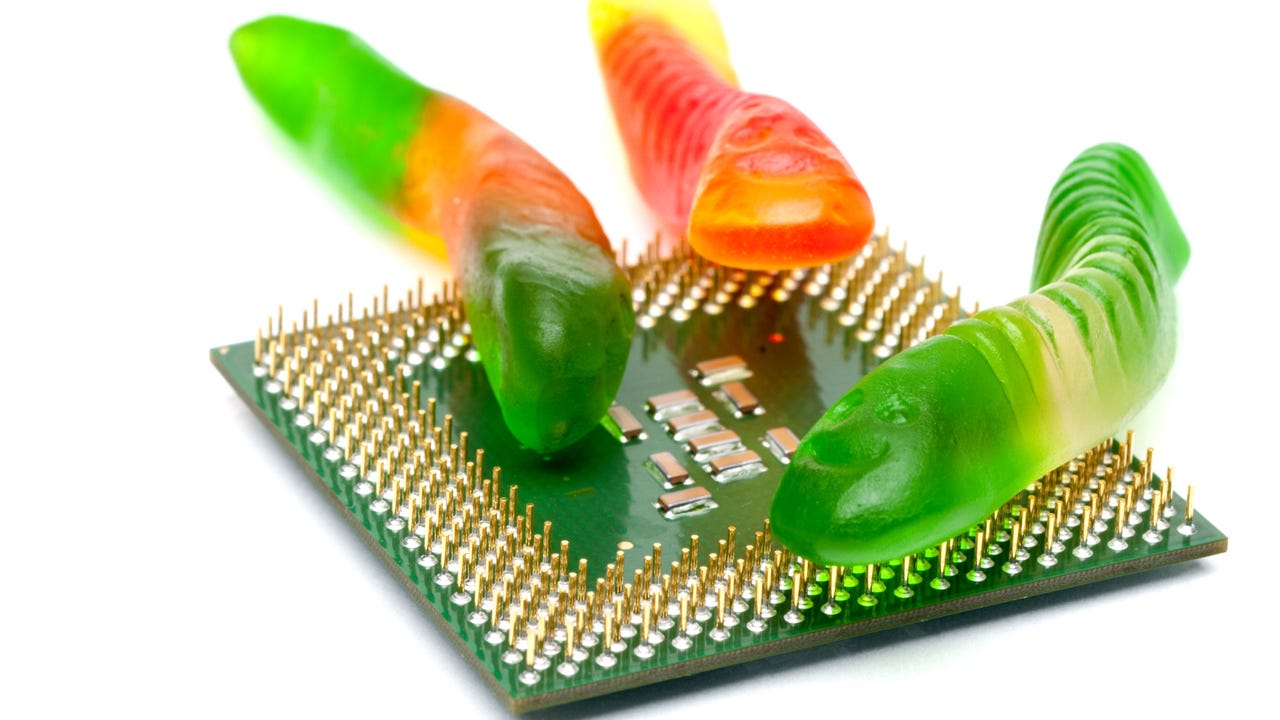
How GlassWorm wormed its way back into developers’ code — and what it says about open source security
Pervasive, evasive malware thought to have been eliminated has wormed its way back into development environments. Just a little over two weeks after GlassWorm was […]
GlassWorm Returns, Slices Back into VS Code Extensions
GlassWorm, a self-propagating VS Code malware first found in the Open VSX marketplace, continues to infect developer devices around the world. The original article found […]
OWASP Highlights Supply Chain Risks in New Top 10
Security misconfiguration jumped to second place while injection vulnerabilities dropped, as organizations improve defenses against traditional coding flaws. The original article found on darkreading Read […]
Konni Hackers Turn Google’s Find Hub into a Remote Data-Wiping Weapon
The North Korea-affiliated threat actor known as Konni (aka Earth Imp, Opal Sleet, Osmium, TA406, and Vedalia) has been attributed to a new set of […]
Hackers Exploiting Triofox Flaw to Install Remote Access Tools via Antivirus Feature
Google’s Mandiant Threat Defense on Monday said it discovered n-day exploitation of a now-patched security flaw in Gladinet’s Triofox file-sharing and remote access platform. The […]