A financially motivated operation codenamed REF1695 has been observed leveraging fake installers to deploy remote access trojans (RATs) and cryptocurrency miners since November 2023. “Beyond cryptomining, the threat actor monetizes […]
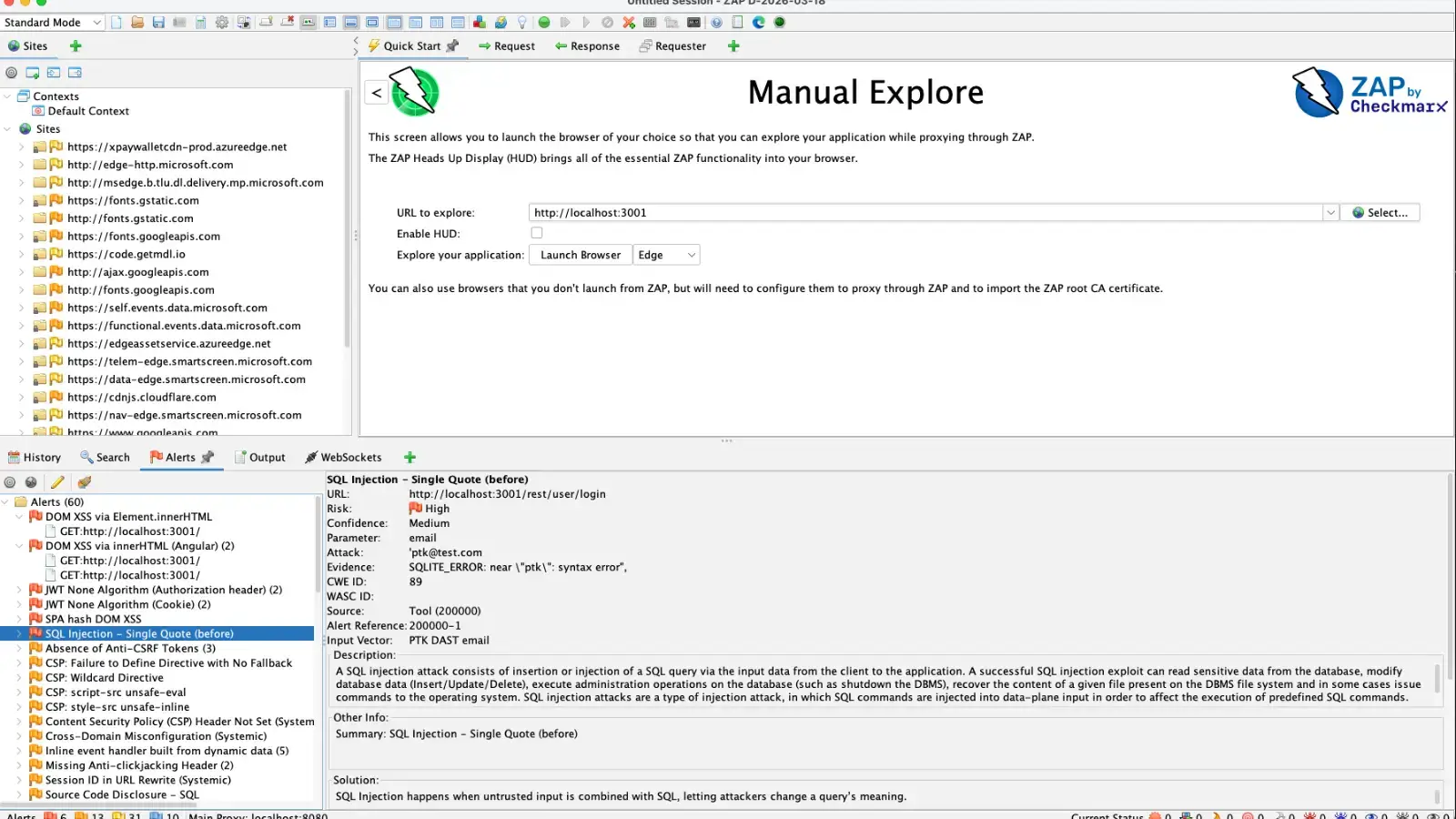
New ZAP PTK Add-On Converts Browser Security Findings Into Native ZAP Alerts
The OWASP Zed Attack Proxy (ZAP) just received a massive upgrade for testing modern web applications. The release of the ZAP PTK Add-on 0.3.0, working […]
FBI Warns Chinese Mobile Apps Could Expose User Data to Cyberattacks
The Federal Bureau of Investigation (FBI) has issued a public warning about potential data security risks associated with foreign-developed mobile applications, particularly those developed by […]
Cybersecurity in the age of instant software
AI is rapidly changing how software is written, deployed, and used. Trends point to a future where AIs can write custom software quickly and easily: […]
Axios npm Supply Chain Breach: Microsoft Shares Mitigation Steps
Microsoft has detailed how organizations can detect and mitigate a recent supply chain compromise involving malicious Axios npm releases and infrastructure attributed to the North […]
Apple Releases iOS 18.7.7 Update to Defend Against DarkSword Exploit
Apple has officially expanded the rollout of iOS 18.7.7 and iPadOS 18.7.7 to defend users against a critical web-based threat known as the DarkSword exploit. […]
CISA Issues Alert on Chrome Zero-Day Under Active Exploitation
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued an urgent warning regarding a critical zero-day vulnerability affecting Google Chrome and other Chromium-based web […]
NoVoice on Google Play Exploits 22 Flaws to Hit Millions of Android Users
NoVoice is a new Android rootkit campaign that hid in more than 50 apps on Google Play, exploiting 22 vulnerabilities to hijack millions of older […]
WhatsApp Alerts 200 Users After Fake iOS App Installed Spyware; Italian Firm Faces Action
Meta-owned messaging platform WhatsApp said it alerted about 200 users who were tricked into installing a bogus version of its iOS app that was infected […]
RFQ Malware Campaign Uses DOCX, RTF, JS, and Python
Hackers are abusing DOCX, RTF, JavaScript, PowerShell, and Python to deliver an in‑memory Cobalt Strike beacon in a stealthy spear‑phishing campaign that impersonates Boeing procurement […]