The proliferation of generative AI (GenAI) platforms has revolutionized web-based services, enabling rapid code assistance, natural language processing, chatbot deployment, and automated site construction. However, […]
Experts Find AI Browsers Can Be Tricked by PromptFix Exploit to Run Malicious Hidden Prompts
Cybersecurity researchers have demonstrated a new prompt injection technique called PromptFix that tricks a generative artificial intelligence (GenAI) model into carrying out intended actions by […]
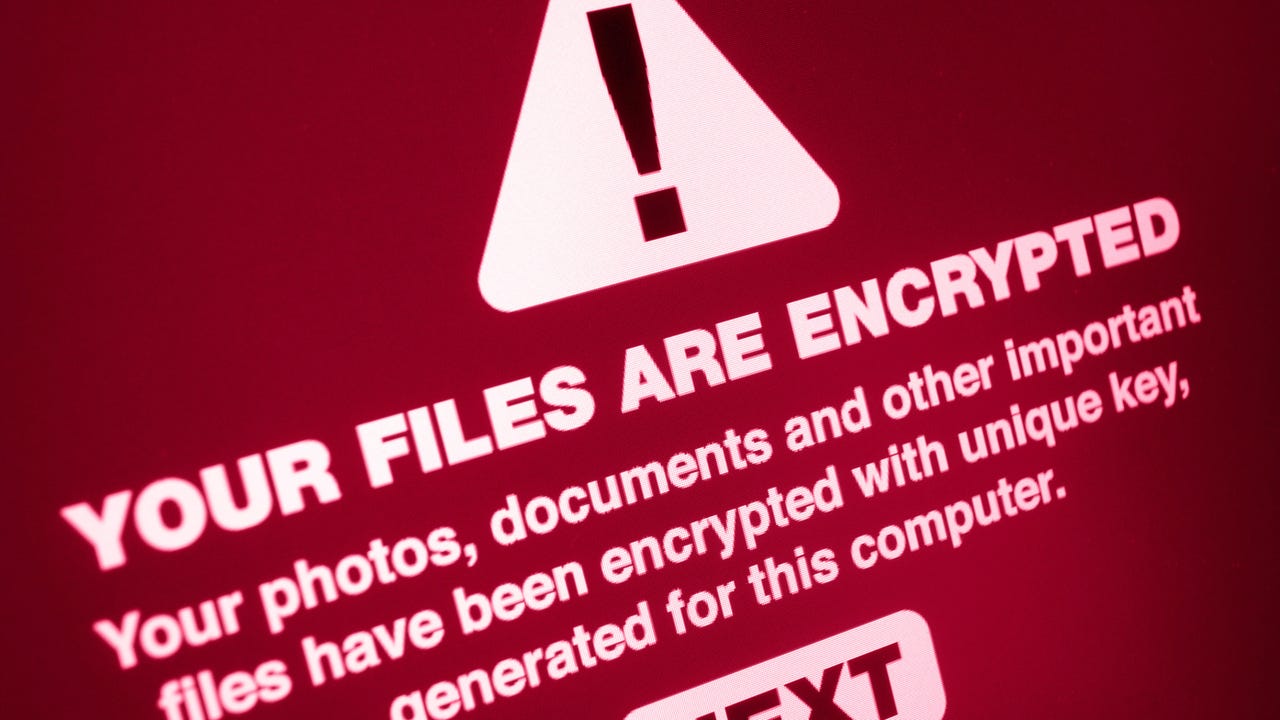
Europe’s Ransomware Surge Is a Warning Shot for US Defenders
We can strip attackers of their power by implementing layered defenses, ruthless patch management, and incident response that assumes failure and prioritizes transparency. The original […]
Scaly Wolf Unleashing Attacks to Expose Organizations’ Hidden Secrets
The Scaly Wolf advanced persistent threat (APT) gang has once again targeted a Russian engineering company in a sophisticated targeted attack that was discovered by […]
CERT/CC Issues Alert on Critical Flaws in Workhorse Municipal Accounting Software
The Computer Emergency Response Team Coordination Center (CERT/CC) has issued a critical security advisory warning of severe vulnerabilities in Workhorse Software Services’ municipal accounting software […]
Serial Hacker Sentenced for Defacing and Hacking Organizational Websites
Al-Tahery Al-Mashriky, 26, of Rotherham, South Yorkshire, was given a 20-month prison sentence for several charges of illegal computer access and data exfiltration, part of […]
Legitimate Chrome VPN with 100K+ Installs Secretly Captures Screenshots and Exfiltrates Sensitive Data
A Chrome extension marketed as FreeVPN.One, boasting over 100,000 installations, a verified badge, and featured placement in the Chrome Web Store, has been exposed as […]
Lenovo chatbot breach highlights AI security blind spots in customer-facing systems
Critical vulnerabilities have been found in Lenovo’s AI-powered customer support chatbot that allowed attackers to steal session cookies and potentially gain unauthorized access to the […]
Copilot Vulnerability Lets Attackers Bypass Audit Logs and Gain Hidden Access
A critical vulnerability in Microsoft’s M365 Copilot allowed users to access sensitive files without leaving any trace in audit logs, creating significant security and compliance […]
🕵️ Webinar: Discover and Control Shadow AI Agents in Your Enterprise Before Hackers Do
Do you know how many AI agents are running inside your business right now? If the answer is “not sure,” you’re not alone—and that’s exactly […]