Cybersecurity risks can come from everywhere, as these riveting Dark Reading News Desk videos detail. Check out Part 1 of our broadcast coverage of the […]
Russian Hacktivists Take Aim at Polish Power Plant, Again
This attack was seemingly more successful than the first iteration, causing disruptions at the plant. The original article found on darkreading Read More
‘RingReaper’ Sneaks Right Past Linux EDRs
The highly sophisticated post-compromise tool abuses the Linux kernel’s io_uring interface to remain hidden from endpoint detection and response systems. The original article found on […]
How to Vibe Code With Security in Mind
As more organizations integrate vibe coding and AI-assisted coding into their application development processes, it’s important to remember to put security first. The original article […]
47,000 Individuals Affected by Data Breach, Reveals NY Business Council
The Business Council of New York State, Inc., a prominent commercial organization based in Albany, has disclosed a data breach impacting approximately 47,329 individuals. The […]
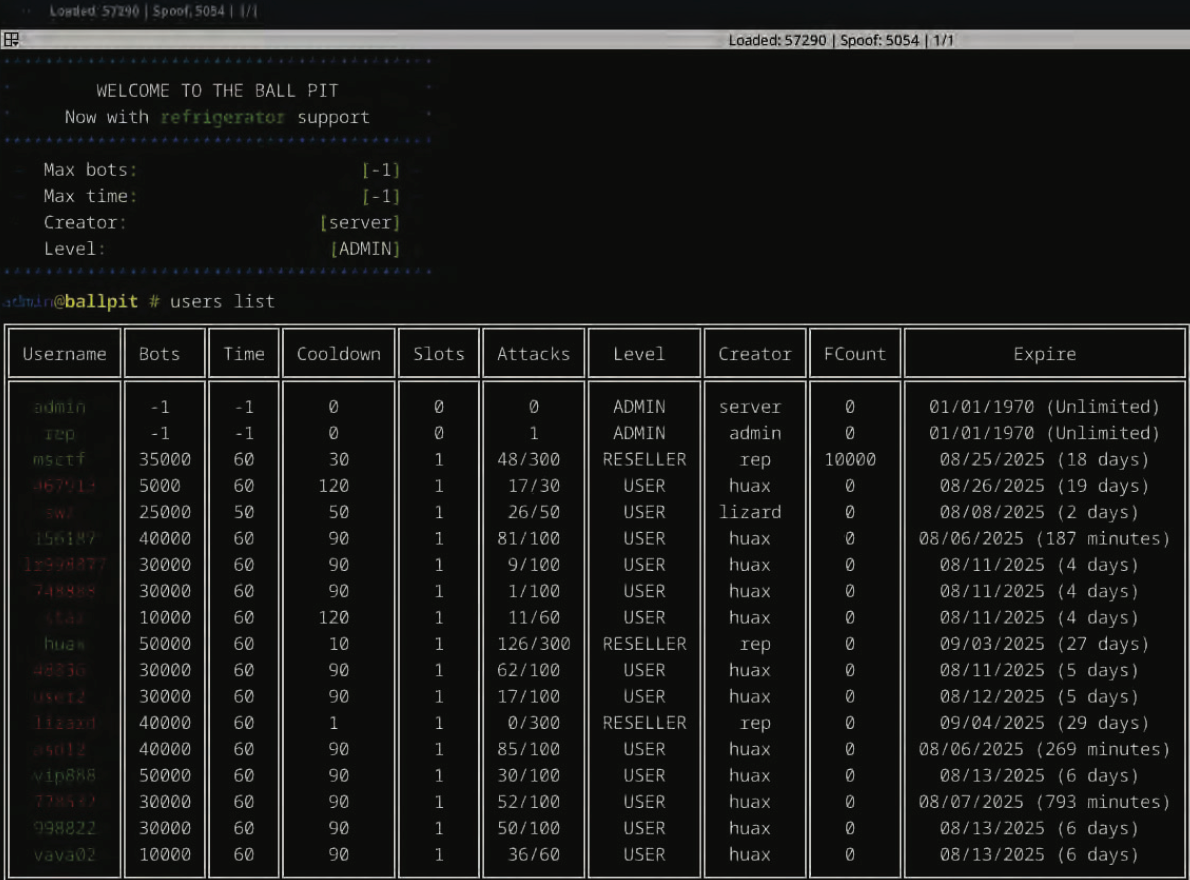
Oregon Man Charged in ‘Rapper Bot’ DDoS Service
A 22-year-old Oregon man has been arrested on suspicion of operating “Rapper Bot,” a massive botnet used to power a service for launching distributed denial-of-service […]
AI Agents Access Everything, Fall to Zero-Click Exploit
Zenity CTO Michael Bargury joins the Black Hat USA 2025 News Desk to discuss research on a dangerous exploit, how generative AI technology has “grown […]
Surprise departure of Oracle security chief as company shifts focus to AI
Oracle’s veteran chief security officer Mary Ann Davidson is leaving the company unexpectedly, ending a career in senior management spanning almost four decades. A prominent […]
New Research Exposes DPRK IT Workers’ Email Addresses and Recruitment Trends
New cybersecurity research has revealed important details about how DPRK-affiliated IT professionals, who fall under Microsoft’s “Jasper Sleet” threat actor group, operate. They take advantage […]
New Research Reveals Security Vulnerabilities Linked to Popular VPN Apps
Researchers have uncovered deceptive practices among major VPN providers, linking seemingly independent entities into three distinct “families” with combined Google Play Store downloads exceeding 700 […]