Cybersecurity researchers have disclosed details of a new phishing campaign that conceals malicious payloads by abusing link wrapping services from Proofpoint and Intermedia to bypass […]
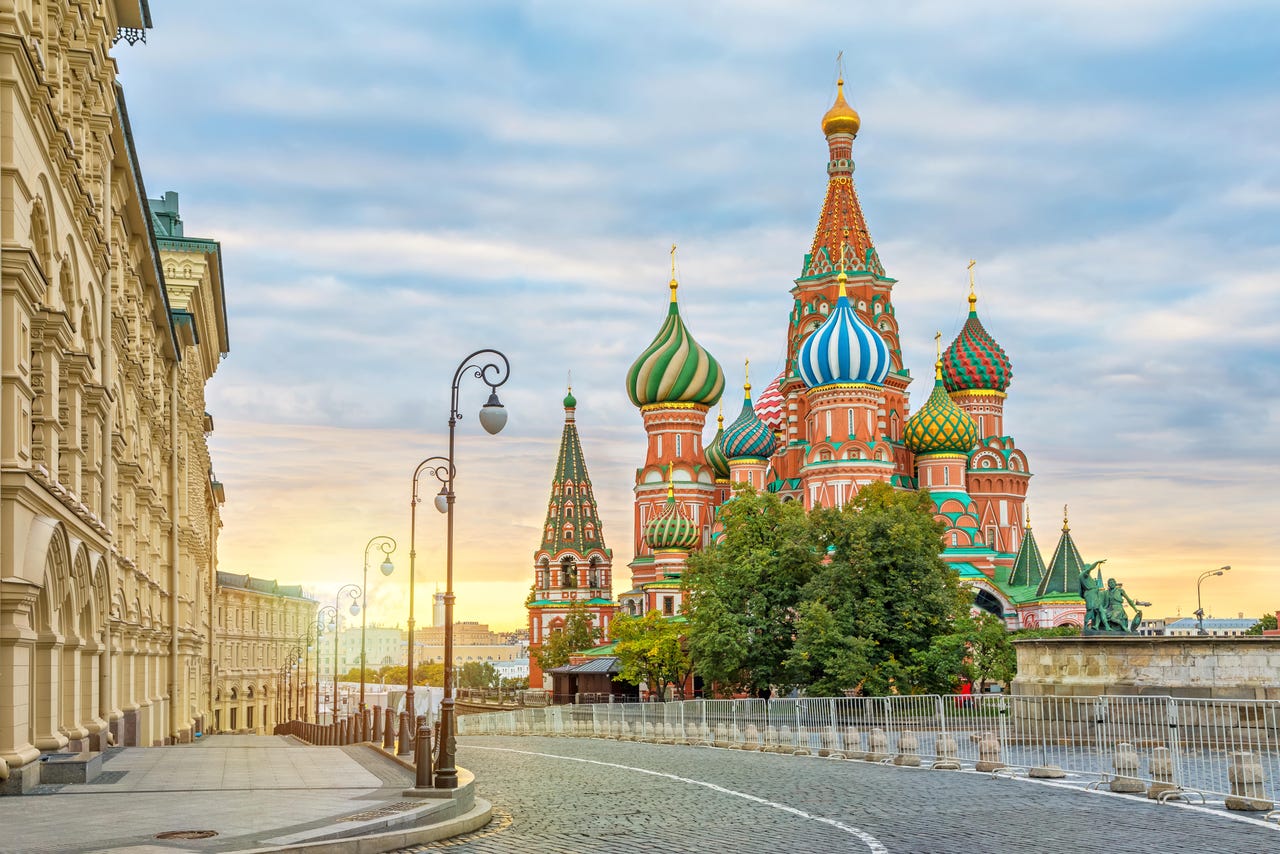
Russia’s Secret Blizzard APT Gains Embassy Access via ISPs
An ongoing AitM campaign by the infamous Moscow-sponsored cyber threat actor has widened its scope, dropping the dangerous ApolloShadow custom backdoor malware thanks to lawful […]
The CrowdStrike Outage Was Bad, but It Could Have Been Worse
A year after the largest outage in IT history, organizations need to make an active effort to diversify their technology and software vendors and create […]
Threat Actors Use LNK Files to Deploy RedLoader Malware on Windows Systems
Sophos analysts have identified a novel infection chain employed by the financially motivated cybercriminal group GOLD BLADE, also known as RedCurl, Red Wolf, and Earth […]
Hackers Deploy Cobalt Strike Beacon Using GitHub and Social Media
A sophisticated cyberattack campaign disrupted the Russian IT industry and entities in several other countries, leveraging advanced evasion techniques to deploy the notorious Cobalt Strike […]
Palo Alto kauft CyberArk
Der israelische Identity-Management-Anbieter CyberArk wird Teil von Palo Alto Networks. ShU studio | shutterstock.com Mit der Übernahme des Identity-Management-Spezialisten CyberArk für rund 25 Milliarden Dollar […]
Qilin Ransomware Uses TPwSav.sys Driver to Bypass EDR Security Measures
Cybercriminals affiliated with the Qilin ransomware-as-a-service (RaaS) operation have demonstrated advanced evasion techniques by exploiting a previously undocumented vulnerable driver, TPwSav.sys, to disable Endpoint Detection […]
LLM Honeypots Can Deceive Threat Actors into Exposing Binaries and Known Exploits
Large language model (LLM)-powered honeypots are becoming increasingly complex instruments for luring and examining threat actors in the rapidly changing field of cybersecurity. A recent […]
Palo Alto Networks to buy CyberArk for $25B as identity security takes center stage
Palo Alto Networks is making what could be its biggest bet yet by agreeing to buy Israeli identity security company CyberArk for around $25 billion. […]
Game changer: How AI simplifies implementation of Zero Trust security objectives
As enterprises increasingly move workloads to private cloud for reasons such as performance and compliance and to leverage AI on-premises, security leaders face a critical […]