Post Content The original article found on darkreading Read More
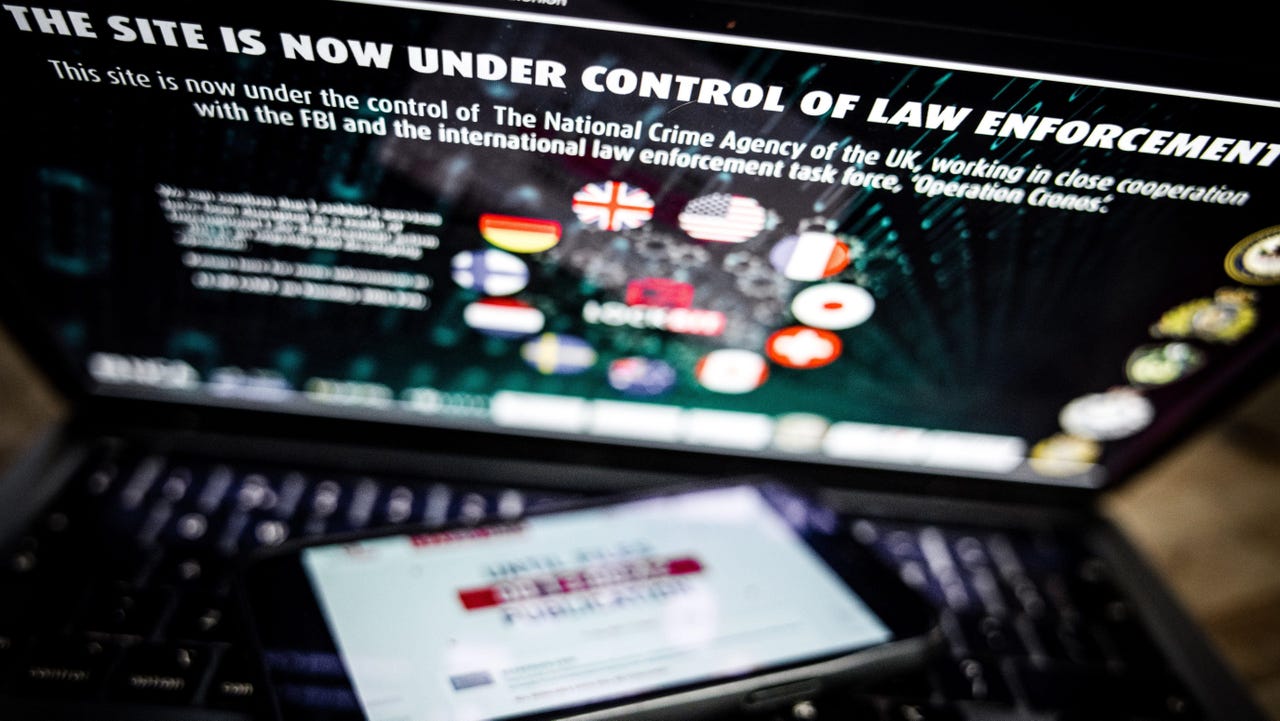
LockBit Ransomware Gang Hacked, Operations Data Leaked
Exposed data from LockBit’s affiliate panel includes Bitcoin addresses, private chats with victim organizations, and user information such as credentials. The original article found on […]
Cyber Then & Now: Inside a 2-Decade Industry Evolution
On Dark Reading’s 19-year anniversary, Editor-in-Chief Kelly Jackson Higgins stops by Informa TechTarget’s RSAC 2025 Broadcast Alley studio to discuss how things have changed since […]
OtterCookie v4 Adds VM Detection and Chrome, MetaMask Credential Theft Capabilities
The North Korean threat actors behind the Contagious Interview campaign have been observed using updated versions of a cross-platform malware called OtterCookie with capabilities to […]
BREAKING: 7,000-Device Proxy Botnet Using IoT, EoL Systems Dismantled in U.S. – Dutch Operation
A joint law enforcement operation undertaken by Dutch and U.S. authorities has dismantled a criminal proxy network that’s powered by thousands of infected Internet of […]
Cyberattackers Targeting IT Help Desks for Initial Breach
Cybercriminals are increasingly impersonating IT support personnel and trusted authorities to manipulate victims into granting access to critical systems, according to recent analyses by cybersecurity […]
Insight Partners Data Breach: Bigger Impact Than Anticipated
The investigation is ongoing, but the VC giant intends to inform affected customers on a rolling basis as more of the breach details come to […]
Threat Actors Target Job Seekers with Three New Unique Adversaries
Netcraft has uncovered a sharp rise in recruitment scams in 2024, driven by three distinct threat actors employing unique and highly technical strategies to exploit […]
Hackers Weaponizing Facebook Ads to Deploy Multi-Stage Malware Attacks
A persistent and highly sophisticated malvertising campaign on Facebook has been uncovered by Bitdefender Labs, exploiting the trust associated with major cryptocurrency exchanges to distribute […]
New Stealthy .NET Malware Hiding Malicious Payloads Within Bitmap Resources
Cybersecurity researchers at Palo Alto Networks’ Unit 42 have uncovered a novel obfuscation method employed by threat actors to conceal malware within bitmap resources of […]