A critical security flaw has been disclosed in Apache Tika that could result in an XML external entity (XXE) injection attack. The vulnerability, tracked as […]
MuddyWater Hackers Use UDPGangster Backdoor to Bypass Network Defenses on Windows
The MuddyWater threat group has escalated its cyber espionage operations by deploying UDPGangster, a sophisticated UDP-based backdoor designed to infiltrate Windows systems while systematically evading […]
Threat Actors Distribute CoinMiner Malware through USB Drives to Infect Workstations
Cybercriminals continue to exploit USB drives as infection vectors, with recent campaigns delivering sophisticated CoinMiner malware that establishes persistent cryptocurrency-mining operations on compromised workstations. Security […]
Avast Antivirus Sandbox Vulnerabilities Allow Privilege Escalation
SAFA researchers uncovered four kernel heap overflow vulnerabilities in Avast Antivirus’s aswSnx.sys driver, designated CVE-2025-13032, affecting versions before 25.3 on Windows. These flaws originate from […]
Chinese Hackers Have Started Exploiting the Newly Disclosed React2Shell Vulnerability
Two hacking groups with ties to China have been observed weaponizing the newly disclosed security flaw in React Server Components (RSC) within hours of it […]
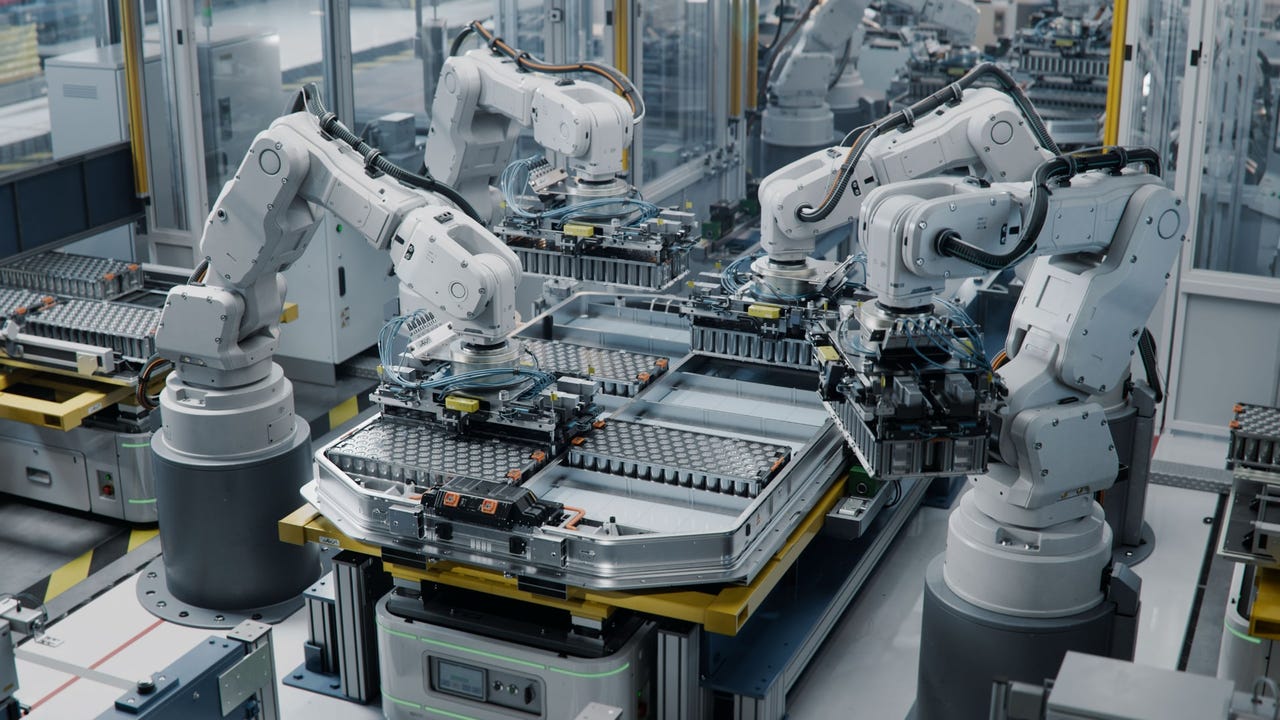
Threat Landscape Grows Increasingly Dangerous for Manufacturers
Manufacturers are the top target for cyberattacks in 2025 because of their still-plentiful cybersecurity gaps and a lack of expertise. The original article found on […]
Ransomware: Trotz besserer Abwehr hoher Anteil an Lösegeldzahlungen
srcset=”https://b2b-contenthub.com/wp-content/uploads/2025/12/shutterstock_2409735251.jpg?quality=50&strip=all 6485w, https://b2b-contenthub.com/wp-content/uploads/2025/12/shutterstock_2409735251.jpg?resize=300%2C168&quality=50&strip=all 300w, https://b2b-contenthub.com/wp-content/uploads/2025/12/shutterstock_2409735251.jpg?resize=768%2C432&quality=50&strip=all 768w, https://b2b-contenthub.com/wp-content/uploads/2025/12/shutterstock_2409735251.jpg?resize=1024%2C576&quality=50&strip=all 1024w, https://b2b-contenthub.com/wp-content/uploads/2025/12/shutterstock_2409735251.jpg?resize=1536%2C864&quality=50&strip=all 1536w, https://b2b-contenthub.com/wp-content/uploads/2025/12/shutterstock_2409735251.jpg?resize=2048%2C1152&quality=50&strip=all 2048w, https://b2b-contenthub.com/wp-content/uploads/2025/12/shutterstock_2409735251.jpg?resize=1240%2C697&quality=50&strip=all 1240w, https://b2b-contenthub.com/wp-content/uploads/2025/12/shutterstock_2409735251.jpg?resize=150%2C84&quality=50&strip=all 150w, https://b2b-contenthub.com/wp-content/uploads/2025/12/shutterstock_2409735251.jpg?resize=854%2C480&quality=50&strip=all 854w, https://b2b-contenthub.com/wp-content/uploads/2025/12/shutterstock_2409735251.jpg?resize=640%2C360&quality=50&strip=all 640w, https://b2b-contenthub.com/wp-content/uploads/2025/12/shutterstock_2409735251.jpg?resize=444%2C250&quality=50&strip=all 444w” width=”1024″ height=”576″ sizes=”auto, […]
AI in CI/CD pipelines can be tricked into behaving badly
AI agents embedded in CI/CD pipelines can be tricked into executing high-privilege commands hidden in crafted GitHub issues or pull request texts. Researchers at Aikido […]
Avoiding the next technical debt: Building AI governance before it breaks
The AI rush is repeating a familiar mistake. Early in my career, a risk executive I worked with used to say, “You didn’t invite me […]
CISOs Should Be Asking These Quantum Questions Today
As quantum quietly moves beyond lab experiment and into production workflows, here’s what enterprise security leaders should be focused on, according to Lineswala. The original […]


.webp?ssl=1)